Most security strategies are built around a clear assumption.
Threats come from the outside.
Firewalls, network monitoring, perimeter defenses, identity controls. All critical. All necessary.
But increasingly, that’s not where problems begin.
They begin at the endpoint.
A download that shouldn’t have happened.
A file that looks harmless but isn’t.
A behavior that doesn’t match normal usage patterns.
Small signals. Easy to miss. Often ignored.
Until they aren’t.
The Endpoint Is Where Reality Happens
Security models often focus on infrastructure.
Servers. Networks. Gateways.
But actual work happens on devices.
Files are downloaded
Applications are installed
Links are clicked
Scripts are executed
This is where intent meets execution.
And this is where early signals of risk appear.
Not Every Threat Looks Like an Attack
The challenge is that most risky activity doesn’t look dramatic.
It doesn’t trigger alarms immediately.
It looks like:
A file downloaded from a new source
An application behaving slightly differently than usual
A process consuming resources in an unexpected way
A user action outside their typical pattern
Individually, these don’t always cross predefined thresholds.
But they are signals.
Signals that something may be off.
The Gap Between Detection and Action
Many organizations already collect endpoint data.
Logs. Events. Telemetry.
But there’s a gap.
Data is available.
Context is missing.
Action is delayed.
Security teams are often left with:
Too many low-confidence signals
Too little clarity on what matters
Too much reliance on manual investigation
By the time something is clearly identified as a threat, the window for early intervention may have passed.
Why Traditional Approaches Fall Short
Most security systems are designed around known patterns.
Signatures. Rules. Indicators of compromise.
They work well for known threats.
They struggle with:
New or evolving behaviors
Subtle deviations from normal activity
Context-specific anomalies
Endpoints don’t operate in clean, predictable environments.
They are messy, dynamic, and user-driven.
Which means risk often shows up as deviation, not as a known signature.
Detecting Risk as Behavior, Not Event
A more effective approach is to look at behavior over time.
What is normal for this device?
What is typical for this user?
What patterns are consistent across the environment?
Anything that deviates meaningfully from that baseline becomes a signal.
Not necessarily a confirmed threat.
But something worth acting on early.
This shifts security from reactive detection to proactive risk management.
Early Intervention Changes the Outcome
Catching an issue early doesn’t always mean stopping a breach.
Sometimes it means:
Isolating a suspicious process
Blocking access to a risky file
Reverting a configuration change
Alerting with enough context to act quickly
The earlier this happens, the smaller the impact.
And in many cases, the user remains unaffected.
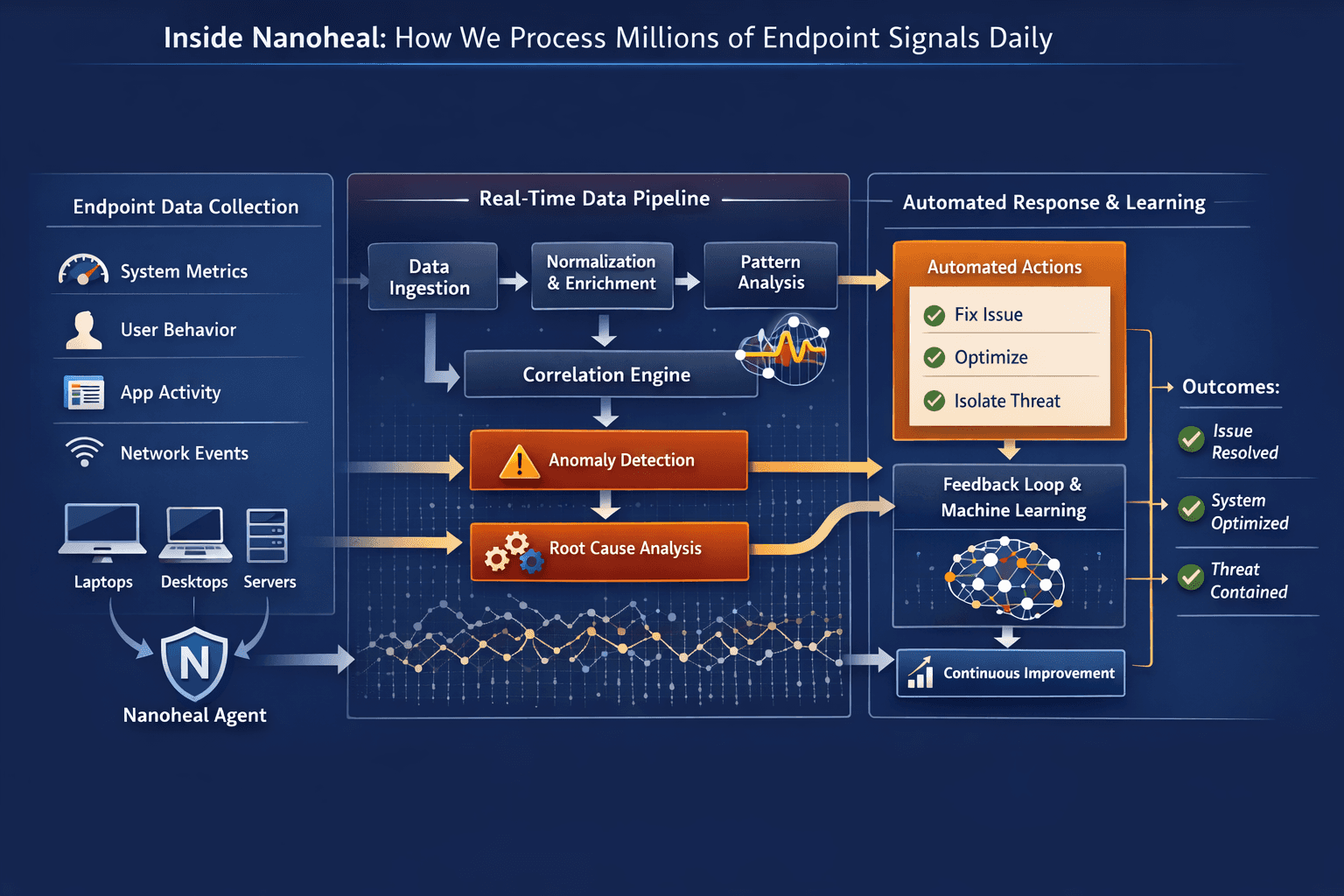
Where Nanoheal Fits In
Nanoheal approaches endpoint security from an operational perspective.
Not as a standalone security layer, but as part of continuous endpoint intelligence.
It focuses on:
Monitoring behavioral patterns across devices
Identifying anomalies that indicate potential risk
Detecting suspicious files and activities early
Taking corrective actions where appropriate
Providing context when escalation is required
Because it already understands how endpoints behave under normal conditions, it can spot when something deviates in a meaningful way.
And more importantly, it can act on it.
Security as a Byproduct of Good Operations
One of the more interesting outcomes of this approach is that security improves as operations improve.
Stable systems are harder to exploit
Consistent configurations reduce attack surface
Early anomaly detection limits exposure
Security stops being a separate function.
It becomes part of how the system operates.
Final Thought
Most breaches don’t start with a catastrophic failure.
They start with a small, unnoticed signal.
Something slightly out of place.
The challenge is not just detecting these signals.
It’s recognizing them early enough to matter.
Because once something becomes obvious, it’s often already too late.